Wow, only a few hours after tweeting that this needed to be “ironed out,” SpecterDev has now released his version of the PS5 IPV6 Kernel exploit.
This release uses the Webkit vulnerability as an entry point. This means that it will work on any PS5 running firmware 4.03, including the PS5 Digital Edition. It might work with lower firmware (although the exploit might need tweaking). At the moment, higher firmware won’t work (they are not vulnerable to the Webkit exploit)
PS5 4.03 Kernel Exploit Is Here
SpecterDev warns that this exploit has some big problems. Notably:
- He has found that the exploit works about 30% of the time. It is not very reliable. Don’t give up if you’re trying to run it. It might take a few tries before the exploit works.
- This exploit lets us read and write, but not execute. This could be more important. This means that there is no way to load and run binaries right now, as everything is limited to the ROP chain. But debug settings can be used with the current implementation.
You Also Check Out These:
- Xbox Release Free Games For October 2022 With Gold
- Diablo 4 Release Date Status PS5: Gameplay, and Design
This is what the exploit’s readme says:
Previously Included
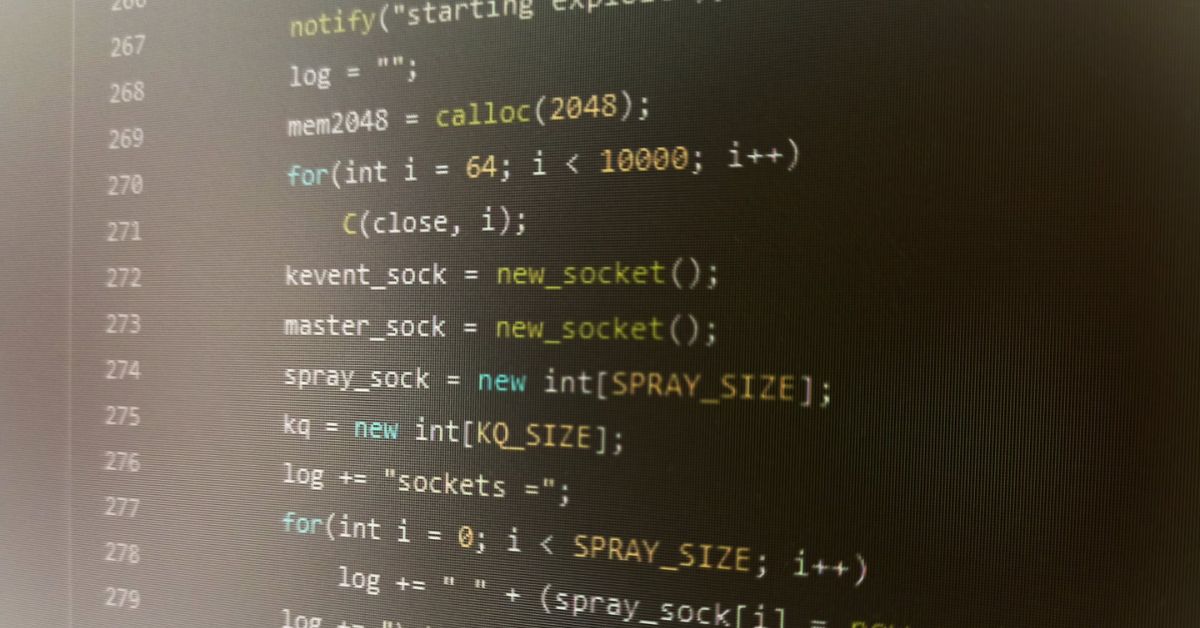
- Obtains arbitrary read/write and can run a basic RPC server for reads/writes (or a dump server for large reads) (must edit your own address/port into the exploit file on lines 673-677)
- Enables debug settings menu (note: you will have to fully exit settings and go back in to see it).
- Gets root privileges
Limitations
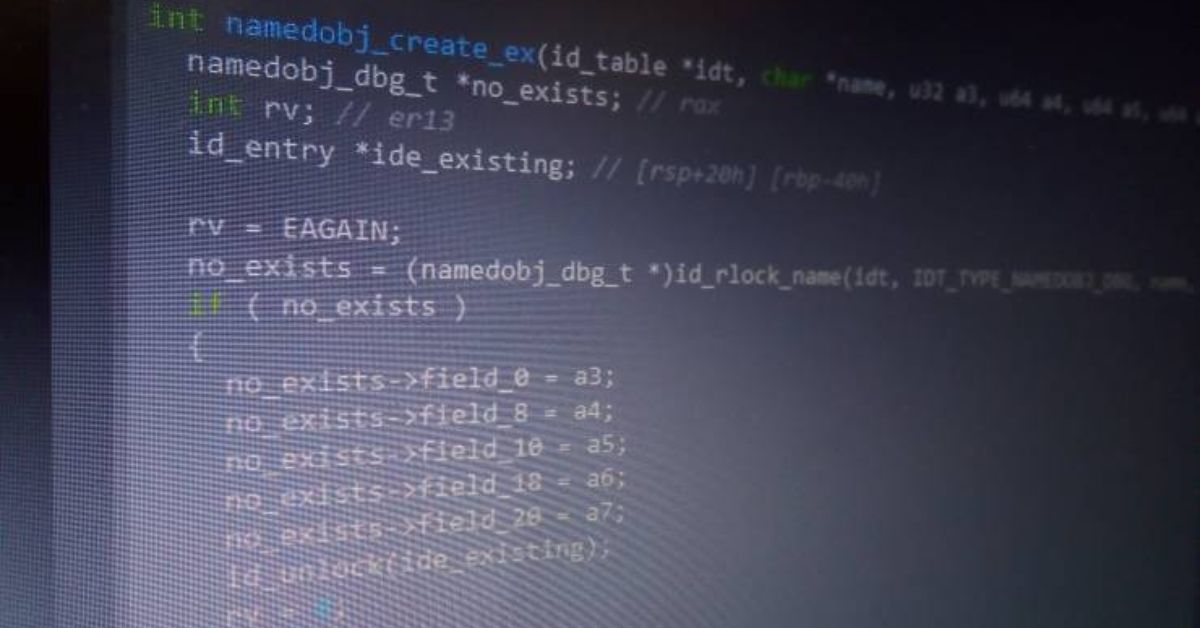
- This exploit achieves read/write, but not code execution. This is because we cannot currently dump kernel code for gadgets, as kernel .text pages are marked as eXecute Only Memory (XOM). Attempting to read kernel .text pointers will panic!
- As per the above + the hypervisor (HV) enforcing kernel write protection, these exploits also cannot install any patches or hooks into kernel space, which means no homebrew-related code for the time being.
- Clang-based fine-grained Control Flow Integrity (CFI) is present and enforced.
- Supervisor Mode Access Prevention/Execution (SMAP/SMEP) cannot be disabled, due to the HV.
- The write primitive is somewhat constrained, as bytes 0x10-0x14 must be zero (or a valid network interface).
- The exploit’s stability is currently poor. More on this is below.
- On a successful run, exit the browser with the circle button, PS button panics for a currently unknown reason.
Notes On Stability
This exploit is only about 30% stable, and there are many places where it could go wrong. In order of observed descending likelihood:
- Stage 1 causes more than one UAF due to failing to catch one or more in the reclaim, causing latent corruption that causes panic sometime later on.
- Stage 4 finds the overlap/victim socket, but the pktopts are the same as the master sockets, causing the “read” primitive to just read back the pointer you attempt to read instead of that pointer’s contents. This needs some improvement and to be fixed if possible because it’s annoying.
- Stage 1‘s attempt to reclaim the UAF fails and something else steals the pointer, causing an immediate panic.
- The kqueue leak fails and it fails to find a recognized kernel .data pointer.
In other words, this release is useful for hackers only, or people who are curious to dig into the inside of the PS5. Note however that despite its limitations, this is the first-ever public release of such a powerful hack for the PS5, which means fresh discoveries are bound to happen!
Video Of PS5 IPV6 Exploitation
Scene member Echo Stretch managed to run the exploit and get us a video of it in action, as can be seen below. In the video, you can see Debug menu and package installer being unlocked on the PS5
Testing PS5 4.03 Kernel Exploit For Disc Or Digital PS5@frwololo @ps4_hacking pic.twitter.com/K8p8j0owoq
— Echo Stretch (@StretchEcho) October 3, 2022
Stay connected to our homepage for more such updates, Journalistpr.com
Leave a Reply